|
1 | 1 | # Security Features |
2 | 2 |
|
3 | | -Devtron provides strong security features that help identify vulnerabilities in container images. The system scans container images thoroughly and generates reports if any vulnerabilities are found. |
| 3 | +{% hint style="info" %} |
| 4 | +### Prerequisite |
4 | 5 |
|
5 | | -Within the CI pipeline of Devtron, there is an option called [**Scan for vulnerabilities**](creating-application/workflow/ci-pipeline.md#scan-for-vulnerabilities). |
| 6 | +Install any one of the following integrations for scanning vulnerabilities: |
| 7 | +* [Clair](../user-guide/integrations/clair.md) |
| 8 | +* Trivy |
| 9 | +{% endhint %} |
6 | 10 |
|
7 | | - |
| 11 | +Devtron's security feature consists of two primary components: |
8 | 12 |
|
9 | | -By enabling this option, the system automatically scans the container image after the image build stage. It then generates a report that highlights all the vulnerabilities present within the image. To access the scan report of all builds with vulnerability scans enabled, simply navigate to the 'Security' tab on the dashboard. There you can conveniently view the build history and all the vulnerabilities detected in the build image. |
| 13 | +1. [Security Scans](./security-features/security-scans.md) - This allows you to identify and address potential security risks effectively. By leveraging this feature, you can ensure that your containerized applications are safeguarded against known vulnerabilities. |
10 | 14 |
|
11 | | - |
12 | | - |
13 | | -The scan report provides a comprehensive overview of any vulnerabilities present in the image. This allows you to identify and address potential security risks effectively. By leveraging this feature, you can ensure that your containerized applications are safeguarded against known vulnerabilities. |
14 | | - |
15 | | -Devtron's Security Feature consists of two primary components: |
16 | | - |
17 | | -1. **Security Scans** |
18 | | -2. **Security Policies** |
19 | | - |
20 | | -## Security Scans |
21 | | - |
22 | | -Devtron's security scans provide comprehensive scan reports for all applications that have undergone vulnerability scanning. These reports offer a detailed overview of the security status of each scanned application. |
23 | | - |
24 | | -These comprehensive scan reports provide valuable insights, including information about identified vulnerabilities, their severity levels, and any corresponding Common Vulnerabilities and Exposures (CVE) entries. |
25 | | - |
26 | | -## Security Policies |
27 | | - |
28 | | -Devtron's Security Policies feature allows users to define policies based on the severity levels of vulnerabilities, which include `Critical`, `Moderate`, and `Low`. Users have the flexibility to set policies that either block the deployment of container images with vulnerabilities or allow their deployment. |
29 | | - |
30 | | -With this feature, users can specify their desired actions for each severity level. For example, they can choose to block any container image with `Critical` vulnerabilities, while allowing container images with `Moderate` or `Low` vulnerabilities to be deployed. |
31 | | - |
32 | | -### Checking Comprehensive Vulnerability Scan Report |
33 | | - |
34 | | -To access the comprehensive security scan reports, follow these steps: |
35 | | - |
36 | | -1. Navigate to the `Security` tab within Devtron. |
37 | | -2. Select the desired application from the available list. |
38 | | - |
39 | | - |
40 | | - |
41 | | -This action will provide detailed information regarding the security scan of the application, including the CVE, Severity of the identified vulnerabilities, as you can see in the image below. |
42 | | - |
43 | | - |
44 | | - |
45 | | -Each vulnerability is identified by a **CVE ID** and categorized based on **Severity**, **Package**, **Current Version**, and **Fixed In Version**. |
46 | | - |
47 | | -* **`CVE ID`** refers to the Common Vulnerability ID assigned to each vulnerability. |
48 | | -* **`Severity`** indicates the severity of the vulnerability and can be classified as Critical, Medium, or Low. |
49 | | -* The **`Package`** column contains metadata associated with the vulnerability. The current Version refers to the specific version of the vulnerability. |
50 | | -* The **`Fixed In Version`** column displays the version name if the vulnerability has been addressed in a subsequent release; otherwise, it remains blank. |
51 | | - |
52 | | -### Discover Vulnerabilities on the Trigger Page |
53 | | - |
54 | | -Devtron provides the capability to identify vulnerabilities before image deployment in the Continuous Deployment (CD) pipeline. This ensures that potential vulnerabilities are detected and addressed early in the deployment process. |
55 | | - |
56 | | -To access security vulnerability details during image deployment in Devtron, follow these steps: |
57 | | - |
58 | | -1. Click on the `Show source info` option for the desired image during the deployment process. |
59 | | -2. Navigate to the `Security` tab. |
60 | | - |
61 | | - |
62 | | - |
63 | | -In the `Security` tab, you will find the security vulnerability details associated with the image. |
64 | | - |
65 | | -**NOTE**: Vulnerabilities will only be displayed if a vulnerability scan has been enabled for that specific image. If no vulnerabilities are visible, it indicates that a vulnerability scan has not been performed for the image. |
66 | | - |
67 | | -### Accessing Vulnerability Information on the App Details Page |
68 | | - |
69 | | -Devtron offers the capability to identify vulnerabilities even after an image has been deployed. By navigating to the `app details` page, you can find comprehensive details about the vulnerabilities associated with the deployed image. |
70 | | - |
71 | | -With this capability, Devtron empowers users to stay informed about the security vulnerabilities present in their deployed images. |
72 | | - |
73 | | - |
74 | | - |
75 | | -By clicking on the 'Details' link in the security vulnerabilities report, you can access detailed information about the security vulnerabilities present inside the deployed image. |
76 | | - |
77 | | -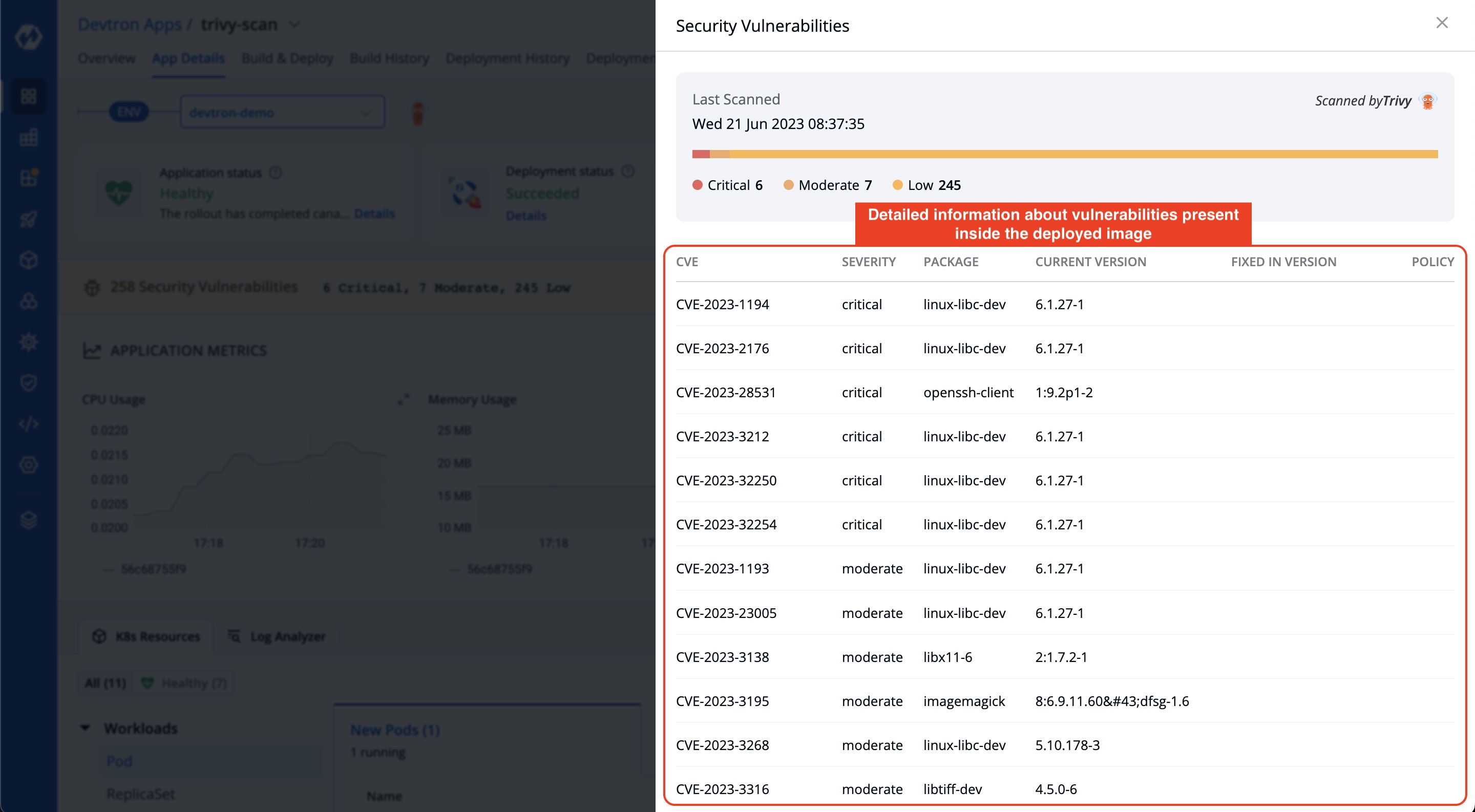 |
78 | | - |
79 | | -## Configuring Security Policies |
80 | | - |
81 | | -You can establish security policies for their vulnerabilities through the `Security Policies` tab, which can be accessed from the left pane by navigating to `Security` and selecting `Security Policies`. Policies are implemented in a hierarchical order, following a specific sequence. The order of implementation is as follows, starting from the highest level: |
82 | | - |
83 | | -* **Global** |
84 | | -* **Cluster** |
85 | | -* **Environment** |
86 | | -* **Application** |
87 | | - |
88 | | -Policies are implemented in a hierarchical order, with the following sequence: Global, Cluster, Environment, and Application. Higher-level policies take precedence over lower-level policies, ensuring a systematic and structured enforcement of security measures. |
89 | | - |
90 | | -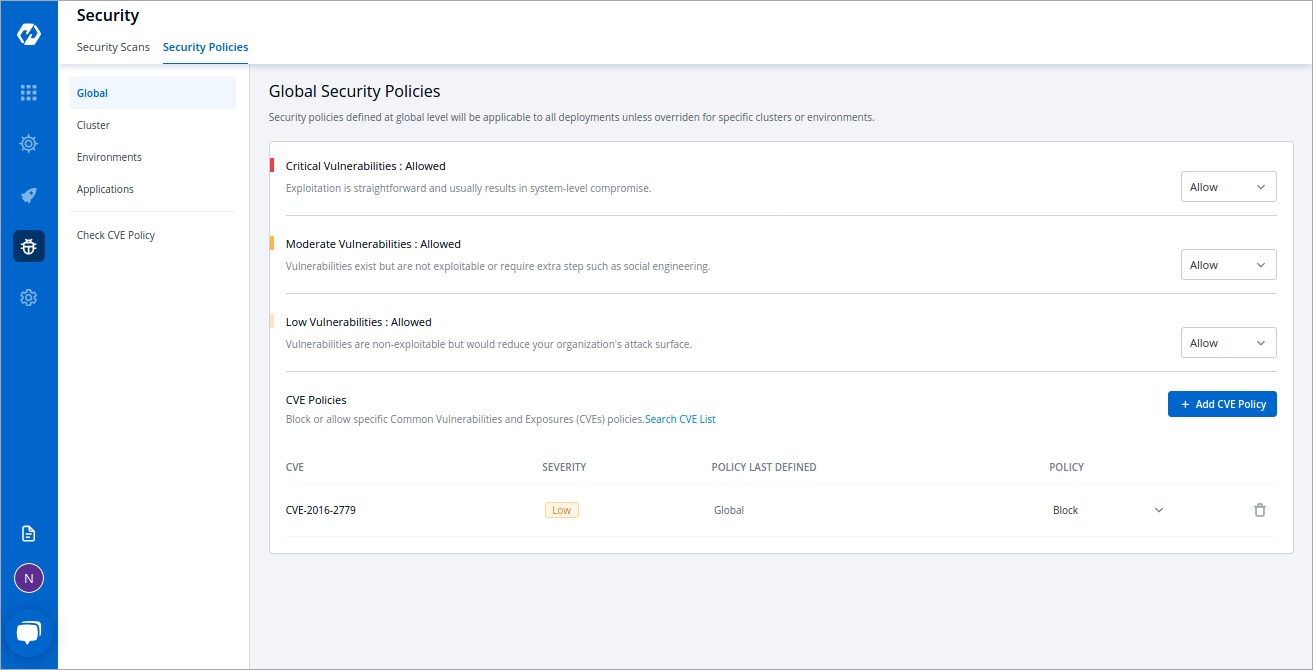 |
91 | | - |
92 | | -**Some examples of how policies can be defined** |
93 | | - |
94 | | -Users can block all the critical vulnerabilities and allow the moderate and low vulnerabilities <br /> |
95 | | -or <br /> |
96 | | -Users can block all vulnerabilities <br /> |
97 | | -or <br /> |
98 | | -Users can block all vulnerabilities for one application and can block only critical vulnerabilities for other applications |
99 | | - |
100 | | -## Configure Global Security Policy |
101 | | - |
102 | | -Within the `Global Security Policies`, there are two options available: Block and Allow. |
103 | | -If critical severity levels are blocked in the `Global Security Policy`, the same blocking will be applied to the `Cluster Security Policy`. Similarly, if the global policy is modified to allow critical levels, it will also allow them in `Cluster Security Policies`. |
104 | | -However, users have the flexibility to explicitly modify these policies as desired. |
105 | | - |
106 | | - |
107 | | - |
108 | | -## Configure Cluster Security Policy |
109 | | - |
110 | | - |
111 | | -In `Global Security Policies`, there are two options: `Block` and `Allow`. `Cluster Security Policies` have an additional option called `Inherit`. |
112 | | - |
113 | | -When `Inherit` is selected, the policy adopts settings from higher-level options. For example, if critical severity levels are blocked globally, they will also be blocked in `Cluster Security Policies`. Changing the global policy to allow critical levels will also allow them in `Cluster Security Policies`. Explicit changes can be made to these policies. |
114 | | - |
115 | | -To block critical vulnerabilities globally but allow them in specific clusters: |
116 | | - |
117 | | -1. Select the desired cluster. |
118 | | -2. Change the critical setting to allow. |
119 | | -3. This change only affects the policy of the selected cluster without impacting others or the global policy. |
120 | | - |
121 | | - |
122 | | - |
123 | | -## Configure Environment Security Policy |
124 | | - |
125 | | -Environment Security Policies, like Cluster Security Policies, offer three options: Block, Allow, and Inherit. |
126 | | - |
127 | | -The `Environment Security Policy` inherits its settings from the `Cluster Security Policy`, following a hierarchical structure where each level inherits the policy from its upper level. |
128 | | - |
129 | | -When you select an environment, it automatically adopts the policy of the associated cluster. For example, if critical-level vulnerabilities are blocked globally but allowed in the `Cluster Security Policy`, the `Environment Security Policy` will inherit this allowance. Consequently, critical-level vulnerabilities will also be allowed in the `Environment Security Policy`. |
130 | | - |
131 | | -However, you have the flexibility to make explicit changes to the policy if needed. This empowers you to customize the policy to align with specific requirements or preferences. |
132 | | - |
133 | | - |
134 | | - |
135 | | -## Configure Application Security Policy |
136 | | - |
137 | | -The `Application Security Policy` operates on a similar principle as other policies. However, in the `Application Security Policy`, the policy is determined by both the Environment option and the Application option. |
138 | | - |
139 | | -When modifying the policy within a development environment, the changes will be applied to all applications within that specific development environment. This means that any adjustments made to the policy settings will be consistently applied across all applications associated with that particular development environment. |
140 | | - |
141 | | -This approach ensures uniformity and streamlined management of security policies within specific environments and their corresponding applications. |
142 | | - |
143 | | - |
144 | | - |
145 | | -## Block or Allow Specific CVE Policies. |
146 | | - |
147 | | -To block or allow specific Common Vulnerabilities and Exposures (CVE) policies, simply click `Add CVE Policy`. |
148 | | - |
149 | | -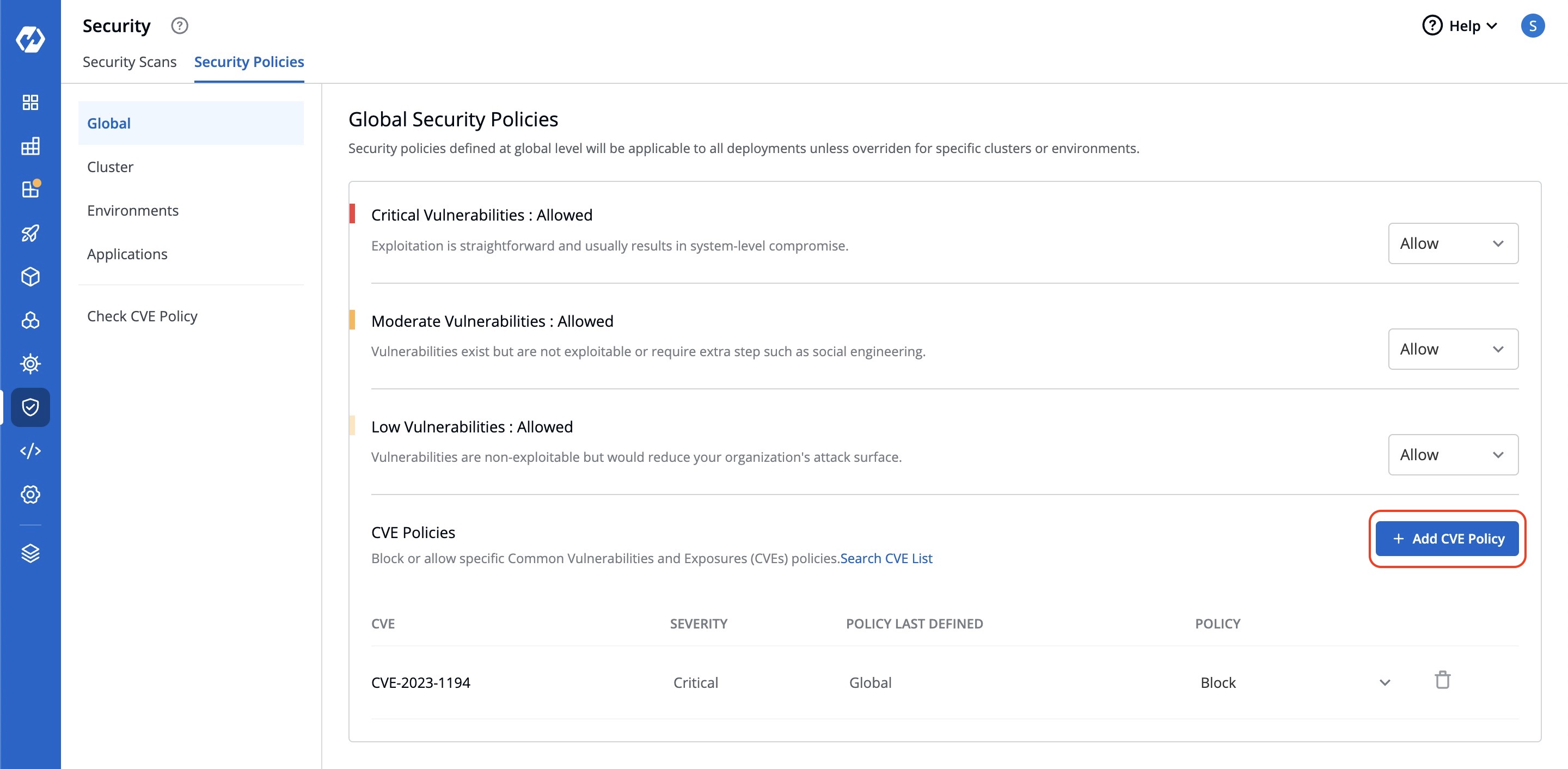 |
150 | | - |
151 | | -A window will appear where you can enter the CVE ID and select whether to allow or block it. |
152 | | - |
153 | | - |
154 | | - |
155 | | -This action will determine whether image deployment is allowed or blocked based on the presence of vulnerabilities matching that particular CVE ID. Any other deployment decisions will be made according to the policies set previously. |
| 15 | +2. [Security Policies](./security-features/security-policies.md) - This allows you to define policies to block or allow the deployment of container images depending on the vulnerabilities detected. |
156 | 16 |
|
| 17 | +{% hint style="warning" %} |
| 18 | +### Who Can Perform This Action? |
| 19 | +Users need to have super-admin permission to enable vulnerability scanning and to define security policies in Devtron. |
| 20 | +{% endhint %} |
0 commit comments